The Role of External Auditors in Improving Cybersecurity Audits in Financial Reporting: A Case Study at PT Pelayaran Logistik Indonesia
DOI:
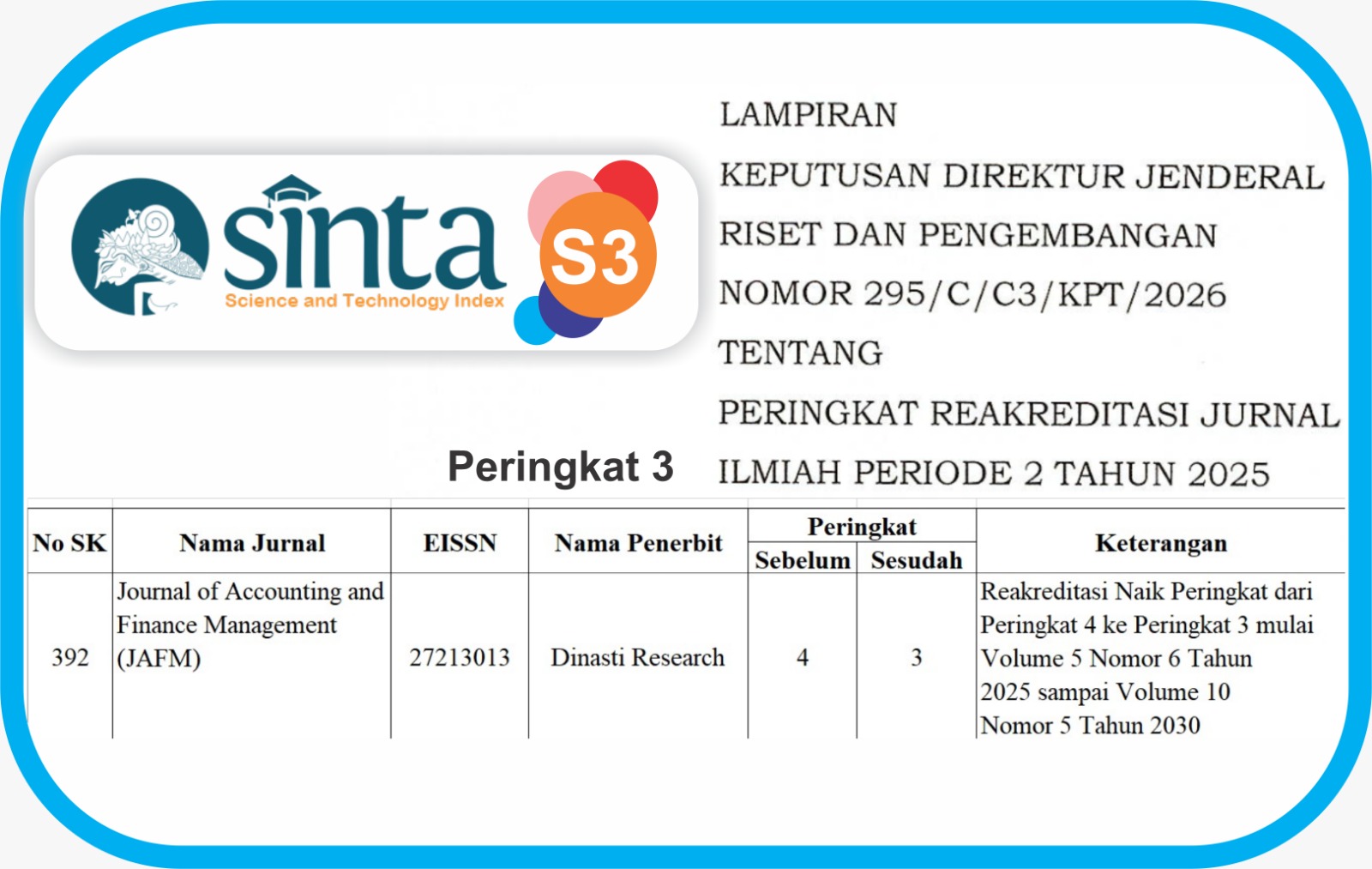
https://doi.org/10.38035/jafm.v7i1.3156Keywords:
External Audit, Cybersecurity, Financial Reporting, Qualitative Research, Digital RiskAbstract
This study explores the role of external auditors in conducting cybersecurity audits and their contribution to improving the quality of financial reporting. Using a qualitative case study approach at PT Pelayaran Logistik Indonesia, a logistics company in Indonesia, data were collected through semi-structured interviews with seven key informants, including external auditors, financial managers, and information technology personnel. Thematic analysis, following Braun and Clarke’s framework, identified three main themes: the strategic role of external auditors in cybersecurity evaluation, the multidimensional challenges of conducting cybersecurity audits, and the effectiveness of cybersecurity audits in enhancing financial statement quality. The findings reveal that external auditors play a critical role in assessing digital security controls, identifying system vulnerabilities, and providing recommendations for technology-based improvements to internal controls. However, auditors face significant challenges, including limited technical competence, restricted access to internal systems, and the absence of explicit regulatory frameworks governing cybersecurity integration in financial audits. Despite these challenges, cybersecurity audits positively impact financial reporting by improving digital documentation, strengthening access controls, and enhancing transparency. This study contributes to the auditing literature by demonstrating the need for cross-disciplinary competence and collaborative audit approaches in the digital era.
References
Abrahams, T. O., Ewuga, S. K., Kaggwa, S., Uwaoma, P. U., Hassan, A. O., & Dawodu, S. O. (2023). Review of strategic alignment: Accounting and cybersecurity for data confidentiality and financial security. World Journal of Advanced Research and Reviews, 20(3), 1743–1756. https://doi.org/10.30574/wjarr.2023.20.3.2691
Alkhalaileh, R., Alshurafat, H., Ananzeh, H., & Al Amosh, H. (2024). The impact of external auditors with forensic accounting competencies on auditee firm performance. Heliyon, 10(11). https://doi.org/10.1016/j.heliyon.2024.e32099
Anjani, N. H. (2021). Perlindungan keamanan siber di Indonesia. Center for Indonesian Policy Studies, 1(9), 1–12. https://doi.org/10.35497/341780
Braun, V., & Clarke, V. (2006). Using thematic analysis in psychology. Qualitative Research in Psychology, 3(2), 77–101. https://doi.org/10.1191/1478088706qp063oa
Braun, V., Clarke, V., Boulton, E., Davey, L., & McEvoy, C. (2021). The online survey is a qualitative research tool. International Journal of Social Research Methodology, 24(6), 641–654. https://doi.org/10.1080/13645579.2020.1805550
Cassell, C., Bishop, V., Symon, G., Johnson, P., & Buehring, A. (2009). Learning to be a qualitative management researcher. Management Learning, 40(5), 513–533. https://doi.org/10.1177/1350507609340811
Chefor, E., Lyngdoh, T., Hochstein, B., Mukundhan, K. V., & Guda, S. (2025). Extending agency theory in sales management: A systematic literature review and future research agenda. Industrial Marketing Management, 125, 195–214. https://doi.org/10.1016/j.indmarman.2025.01.001
Creswell, J. W. (2018). Research design: Qualitative, quantitative, and mixed methods approaches (5th ed.). SAGE Publications.
Demirkan, S., Demirkan, I., & McKee, A. (2020). Blockchain technology in the future of business, cybersecurity, and accounting. Journal of Management Analytics, 7(2), 189–208. https://doi.org/10.1080/23270012.2020.1731721
Di Guimarães, L., Araújo, U. P., & Lima, H. M. de. (2025). Mine closure transparency and disclosure: An open-source evaluation of financial, technical, and social reporting. Resources Policy, 107. https://doi.org/10.1016/j.resourpol.2025.105644
Dunwoodie, K., Macaulay, L., & Newman, A. (2023). Qualitative interviewing in the field of work and organisational psychology: Benefits, challenges and guidelines for researchers and reviewers. Applied Psychology, 72(2), 863–889. https://doi.org/10.1111/apps.12414
Elhawary, E. (2021). Audit committee effectiveness and company performance: Evidence from Egypt. Journal of Governance and Regulation, 10(2), 134–156. https://doi.org/10.22495/JGRV10I2ART12
Fang, J., Liu, Y., & Zhang, R. (2025). IT security controls and material misstatement risk: Evidence from financial audits. Journal of Information Systems, 39(1), 45–67.
Fattah, Moh. A., Zen, B. P., & Wasitarini, D. E. (2023). Penerapan sistem manajemen keamanan informasi ISO 27001 pada Perpusnas RI dalam mendukung keamanan tata kelola teknologi informasi. Jurnal Cyber Security dan Forensic Digital, 6(2), 76–82.
Fatima, F., Hyatt, J. C., Rehman, S. U., De La Cruz, E., Nadella, G. S., & Meduri, K. (2024). Resilience and risk management in cybersecurity: A grounded theory study of emotional, psychological, and organizational dynamics. Journal of Economy and Technology, 2, 247–257. https://doi.org/10.1016/j.ject.2024.08.004
Gulyas, O., & Kiss, G. (2023). Impact of cyber-attacks on the financial institutions. Procedia Computer Science, 219, 84–90. https://doi.org/10.1016/j.procs.2023.01.267
Hays, D. G., & McKibben, W. B. (2021). Promoting rigorous research: Generalizability and qualitative research. Journal of Counseling and Development, 99(2), 178–188. https://doi.org/10.1002/jcad.12365
Kim, R., Hedley, T., Gangolly, J., & Ravi, S. S. (2025). Segregation of duties in accounting systems: A framework. International Journal of Accounting Information Systems, 56. https://doi.org/10.1016/j.accinf.2025.100725
Mubarak, S., & Nagalingam, S. (2021). Factors impacting information security risk management in IT outsourcing: An agency theory perspective. Proceedings of the Pacific Asia Conference on Information Systems (PACIS). https://aisel.aisnet.org/pacis2021
Naeem, M., Ozuem, W., Howell, K., & Ranfagni, S. (2023). A step-by-step process of thematic analysis to develop a conceptual model in qualitative research. International Journal of Qualitative Methods, 22. https://doi.org/10.1177/16094069231205789
Ngo, T. N. B., & Tick, A. (2021). Cybersecurity risk assessments by external auditors. Interdisciplinary Description of Complex Systems, 19(3), 375–390. https://doi.org/10.7906/indecs.19.3.3
Nkansah, E. (2024). Stakeholder engagement in digital security audits: A framework for effective collaboration. International Journal of Auditing, 28(2), 112–130.
Park, S., & Kang, J. (2025). Combating implicit racial bias against hosts in peer-to-peer marketplaces: Insights from availability bias and self-disclosure theory. International Journal of Hospitality Management, 126. https://doi.org/10.1016/j.ijhm.2024.104038
Peng, P., Xie, X., Claramunt, C., Lu, F., Gong, F., & Yan, R. (2025). Bibliometric analysis of maritime cybersecurity: Research status, focus, and perspectives. Transportation Research Part E: Logistics and Transportation Review, 195. https://doi.org/10.1016/j.tre.2025.103971
Roszkowska, P. (2021). Fintech in financial reporting and audit for fraud prevention and safeguarding equity investments. Journal of Accounting and Organizational Change, 17(2), 164–196. https://doi.org/10.1108/JAOC-09-2019-0098
Singh, K., Chatterjee, S., Mariani, M., & Wamba, S. F. (2025). Cybersecurity resilience and innovation ecosystems for sustainable business excellence. Technovation, 143. https://doi.org/10.1016/j.technovation.2025.103219
Siponen, M., Topalli, V., Soliman, W., & Vestman, T. (2025). Reconsidering neutralization techniques in behavioral cybersecurity as cybersecurity hygiene discounting. Computers and Security, 150. https://doi.org/10.1016/j.cose.2024.104306
Downloads
Published
How to Cite
Issue
Section
License
Copyright (c) 2026 Evi Julyanti Situmorang

This work is licensed under a Creative Commons Attribution 4.0 International License.
Authors who publish their manuscripts in this journal agree to the following conditions:
- The copyright on each article belongs to the author(s).
- The author acknowledges that the Journal of Accounting and Finance Management (JAFM) has the right to be the first to publish with a Creative Commons Attribution 4.0 International license (Attribution 4.0 International (CC BY 4.0).
- Authors can submit articles separately, arrange for the non-exclusive distribution of manuscripts that have been published in this journal into other versions (e.g., sent to the author's institutional repository, publication into books, etc.), by acknowledging that the manuscript has been published for the first time in the Journal of Accounting and Finance Management (JAFM).